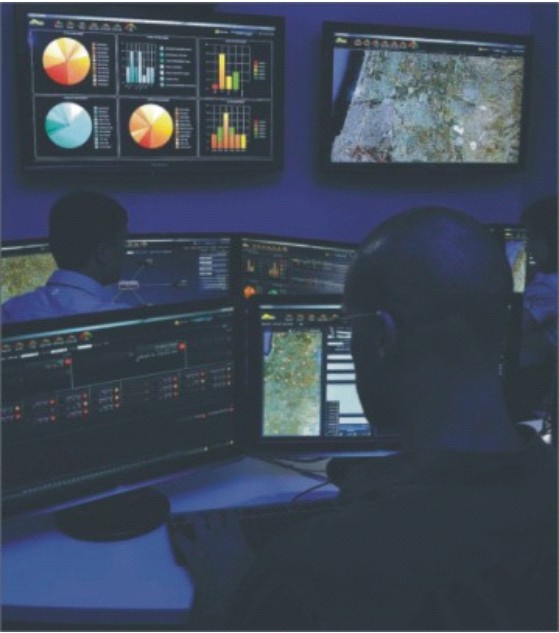
Securing networks
A nation that had acquired a well-earned reputation as a hub of information technology and the seedbed of America’s Silicon Valley start-ups, is slowly wakening to the threat posed by what has come to be known as cyber warfare.
The clandestine use of cyberspace to launch disruptive attacks on networks that have come to rely on the internet, computers and network centricity that affect national security is warfare in a domain different from other traditional battlefields like land, sea, air and space.
The incipient threat was brought home by a series of attacks on sensitive Indian cyber nodes in 2010 and since then the Government of India is trying to plug the loopholes through which Chinese and Pakistani hackers can disable targeted networks through the injection of worms.
This can devastate railways, banks, and commercial activity, adding a new element to the operations of war in the land, air, sea and space domains by inducing paralysis in telecommunications and transportation systems dependent on computer networks.
Sincere efforts
While the armed forces have set up protected networks within their respective network centric links, the threat of penetration and disruption is always present given the changing nature of the threat.
A national effort is underway to deal with not only the military but also the civil aspect of a cyber attack. The Joint Working Group set up after the 2010 attack on the Central Bureau of Investigation website and 6000 other computer presented its report to the government in October this year.
It represents a better-late-than-never situation given that in the major capitals of the world there were storm signals of things to come. Incidentally, a few months before the cyber-raid on the CBI in the US an alarm was raised about the rise in the likelihood of a crippling attack on computer and the telecommunications network dependant on them.
Warnings were also sounded about the widespread nature of the threat encompassing “public and private facilities, banking and finance, transportation and manufacturing, medical, education and government”- all segments in which computers have come to be deeply embedded.
It is a huge swath of the national endeavour that contributes to national security and the ability of a nation to sustain itself in moments of adversity.
It was this aspect that added an element of urgency to the work of the Joint Working Group which was formed in July and submitted its report in October this year. One of its major recommendations closes the gap between what can be described as the governmental sector and the private sector.
It recognized that although Computer Emergency Response Team (CERT) India and the National Technical Research Organisation (NTRO) were designated as the nodal national institutions to deal with the cyber threat they were incapable of dealing with the magnitude of the problem and the dynamic nature of the threat.
The attempt to create sectoral cyber security officers and set up a coordination network through the office of the Deputy National Security Advisor-was deficient in its basic ambiance.
The Indian information technology sector has been a paradox from the moment it caught the imagination of Silicon Valley. The technical infrastructure which lies in the domain of the private sector has been build on software from western sources and hardware from China and Taiwan wherein the Chinese from either side of the Formosa Strait are prime suspects in the hacking of the Indian computer networks.
Hitherto the Indian private sector has created a niche for itself in system integration and project management. Such basic requirements for secrecy and domain security have been the preserve of the much-taunted Defence Research and Development Organisation.
Very little has been done in the private sector to develop indigenous infrastructure for hardware and software development with special reference to the security aspect of networks and computer engendered network centricity.
In hindsight it represents an ongoing hesitation on the part of the private industry to invest in research and development in this particular segment of the IT domain.
The Joint Working Group in its October report has brought forth the necessity of developing synergy in all three aspects of the cyberspace- integration, hardware manufacturing and software creation-with greater private sector participation.
It had included representatives of Government Departments and Agencies from Indian Computer Emergency Response Team (CERT-On), Department of Telecommunications, Ministry of Home Affairs, Ministry of External Affairs, Office of Principal Scientific Adviser (PSA) along with Information and Communication Technology Industry Association including NASSCOM, Data Security Council of India (DSCI), Confederation of Indian Industry (CII), Federation of Indian Chambers of Commerce and Industry (FICCI), Association of Unified Telecom Service Providers of India (AUSPI) and Cellular Operators Association of India (COAI).
Its major recommendations included the setting up of a permanent Joint Working Group under the aegis of National Security Council Secretariat (NSCS) with representatives from government as well as private sector; setting up of the Joint Committee of International Cooperation of Advocacy (JCICA); private companies will set up information Sharing & Analysis Sector (ISACs) in various segments and cooperate with the sectoral Computer Emergency Response Teams (CERTs) at the operational level.
The Joint Working Group identified four pilot projects for collaboration which include:
• Setting up of Pilot Testing Lab.
• Conducting a test audit of a specified sector.
• Studying vulnerabilities in a sample critical information infrastructure.
• Establishment of the multi-disciplinary Centre of Excellence.
The avowed intention is capacity-building, a phrase that has a familiar ring to it because we have been hearing about it in relation to the working of the DRDO which had the monopoly for R&D in major weapons systems but it took decades before it could produce viable platforms and that too with collaboration with foreign original equipment manufacturers. Hopefully, the JWG will produce better results.
Subimal Bhattacharjee, a commentator on cyberspace and security issues, pointed to a lapse on the part of the JWG pertaining to what he described as ‘sanitisation’ of human resources for cyber security purposes.
“Individuals and institutions have to be certified so that they can work in trusted networks for dedicated research and development in this area and also in operational matters”.
He was clearly hinting at the massive leaks of valuable information by individuals who have passed on Indian secrets to foreign countries. The Naval War Room leak was made possible by a relative of a former Chief of Naval Staff.
Earlier, there were suspicious losses of pendrives relating to operational military matters. His suggestion is clearly germaine to the issue of cyber security because it points to a malaise that facilitates foreign penetration into Indian cyber systems.
Both China and Pakistan have set up cyber warfare brigades to scour the internet and look for loopholes in Indian official websites and indulge in vandalism and planting of worms.
China’s preparedness
China, in fact, appears to be preparing to replicate its “human wave” tactics in cyber warfare as well. In a recent article in the “China Defence Daily” the author has suggested that potentially every Chinese is a cyber warrior.
The author, Huang Chunping, 73, is a key player in China’s space and missile defence programmes and is an expert in defence systems, having served as the director of science and technology for the Beijing Institute of Technology.
Huang outlines three things China needs to do to mobilize this massive army:
“First, China must mobilize a strategic-level network warfare command structure. This structure would include a unified general command structure, a military services command and control structure, and integration and mobilization resources.
Second, each branch of the military would need to have its own cyber-warfare command and control (C&C) organization. The C&C structures for each branch would report to a central authority in the Chinese high command.
These groups would need to carry out simulated combat operations and have the appropriate weapons, equipment and training to carry out realistic training exercises. The exercises would include collaborative strategic level network warfare command organizations within industrial sectors, and have especially strong ties to the information technology sector.
Third, China would need to establish the office of war mobilization. This department would be headed by a network coordinator who would have industry expertise and be able to work with the Defense Ministry’s network warfare team. Combat teams would have distant offensive and defensive capabilities that could change depending on the type of attack being waged.
Offensive capabilities would include launching computer viruses, EMP (electromagnetic pulse) bombs, and tunneling into an adversary’s infrastructures through computer and microchip backdoors. (Backdoors into the US infrastructures are already in place).
“Defensive capabilities would include the use of network scanners, network wiretapping devices (called “sniffers”), password cracking programmes, EMP shielding, firewalls, and anti-virus software.”